Authors:
(1) Anna-Katharina Wickert, Technische Universität Darmstadt, Darmstadt, Germany (wickert@cs.tu-darmstadt.de);
(2) Lars Baumgärtner, Technische Universität Darmstadt, Darmstadt, Germany (baumgaertner@cs.tu-darmstadt.de);
(3) Florian Breitfelder, Technische Universität Darmstadt, Darmstadt, Germany (florian.breitfelder@tu-darmstadt.de);
(4) Mira Mezini, Technische Universität Darmstadt, Darmstadt, Germany (mezini@cs.tu-darmstadt.de).
Table of Links
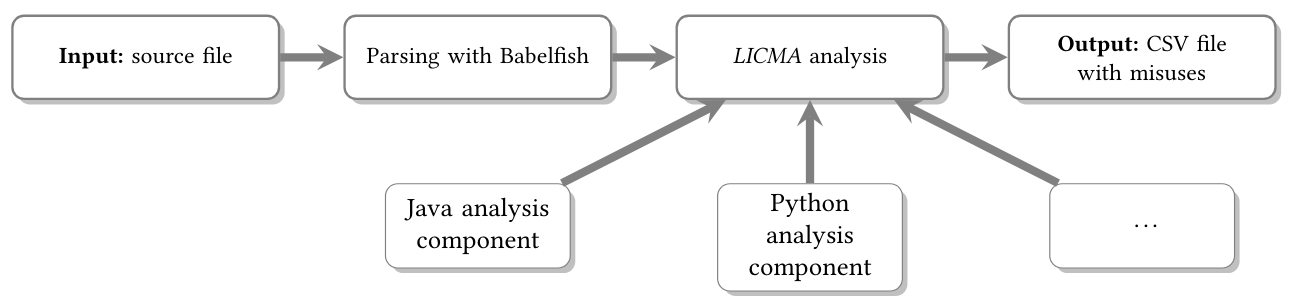
3 Design and Implementation of Licma and 3.1 Design
4 Methodology and 4.1 Searching and Downloading Python Apps
4.2 Comparison with Previous Studies
5 Evaluation and 5.1 GitHub Python Projects
6 Comparison with previous studies
9 Conclusion, Acknowledgments, and References
3.2 Implementation
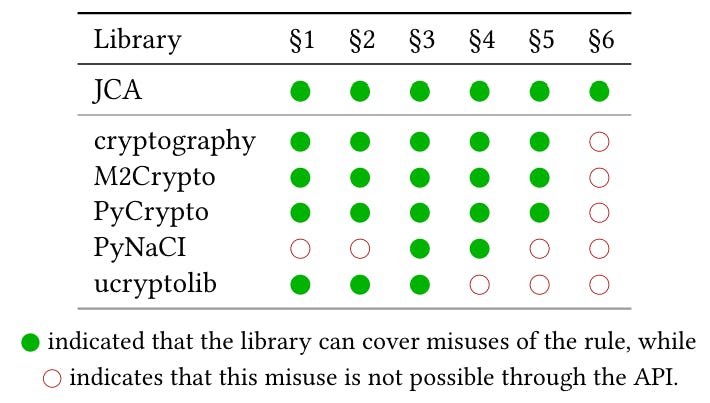
For our study, we implemented Python and Java analysis components. For Python, we cover 5 different crypto modules: cryptography, M2Crypto, PyCrypto, PyNaCl, ucryptolib. This selection is based
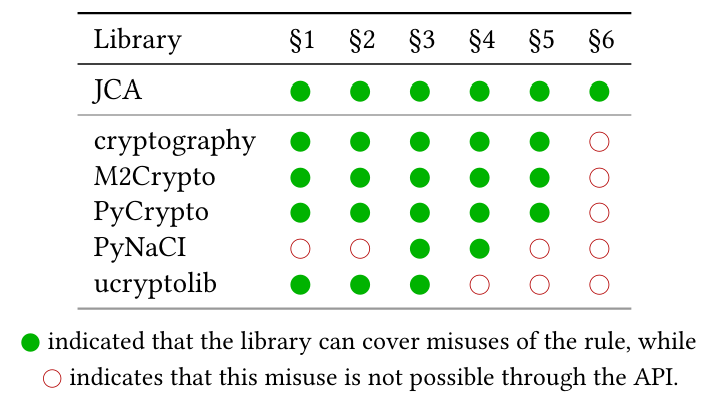
upon the inspected Python modules by Acar et al. [1] which is based on the libraries’ popularity, their possibility to solve common crypto tasks, and a mix of usability focus, e.g., API-design with ignoring usability up to usability as a main focus. However, we dropped the deprecated module Keyczar, and added the MicroPython library ucryptolib.
As the six rules are defined with the JCA in mind [4], we could not implement all of these rules for Python. For none of the Python modules, a misuse of §6 is possible due to the design of the APIs as there are no secure random number generators present that can be initialized with a static seed.
Further, LICMA supports only §3 and §4 for PyNaCl and only §1, §2 and §3 for ucryptolib. The derivation is due to a different API design which avoids the respective misuses. We present an overview of the implemented APIs and the covered rules in Table 2.
Our implementation of LICMA is available on GitHub[4].
This paper is available on arxiv under CC BY 4.0 DEED license.